Currently, news of data breaches appears almost weekly. Many companies have all had their private customer information stolen by hackers. Data breaches occur when hackers infiltrate a company’s data and distribute it to malicious actors on the internet. As more and more of our personal and financial information gets stored online, data breaches have become a really big problem.
A data breach can damage a company’s reputation and incur millions of dollars in fines and cleanup costs. For customers, it means their private information such as social security numbers, addresses, and credit card details can end up for sale on the dark web.
There are ways for companies to protect customer data so it doesn’t get exposed in a breach. One approach is something called “data masking.” Data masking hides real sensitive information by replacing it with fake or “masked” data. This protects the actual data even if hackers break in. Companies can use data masking to avoid data breaches or reduce their impact. In this article, we’ll learn all about how data masking works and how it can help stop data breaches.
What is Data Masking?
Data masking involves replacing real data, such as names, social security numbers, or credit card numbers, with fake data that resembles the original. For example, “John Smith” becomes “Jane Doe,” “123-45-6789” becomes “987-65-4321,” and “1234-5678-9101-1121” becomes “5678-1234-2134-4562.”
The fake masked data looks just such as real data, but it’s not actual customer information. Masking replaces sensitive data with realistic fakes to protect the real data. It’s such as putting a mask over the real data so hackers and unauthorized users can’t see the true values.
Some key things about data masking:
- It hides confidential data such as personal IDs, financials, or health records with fakes.
- The original real data cannot be recovered from the masked data.
- It lets companies share sample customer data for business needs without exposing private details.
- Masking keeps data formats intact, so the fake data works just such as real data.
So, data masking obscures the real sensitive bits with realistic fakes to prevent the actual data from getting stolen or misused.
Data Masking Best Practices
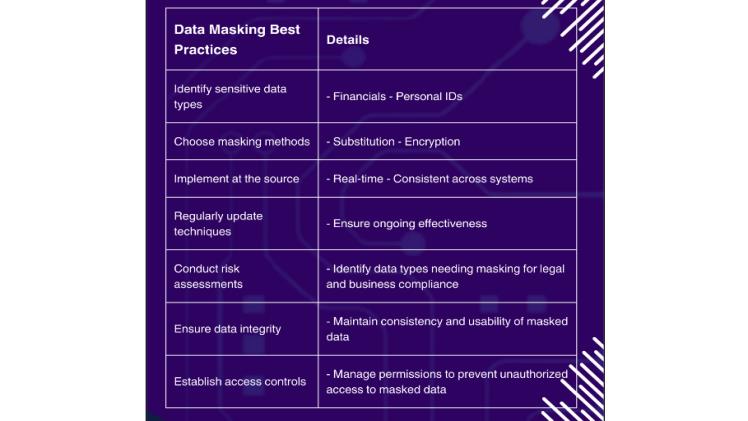
Data masking plays a crucial role in data security, preventing breaches and safeguarding sensitive information. Implementing robust data masking best practices is essential for companies to effectively protect their data assets from unauthorized access or misuse.
By obfuscating or replacing sensitive data with realistic but non-sensitive values, data masking ensures that even if unauthorized individuals gain access to the data, they cannot decipher or misuse it.. This is particularly important in environments where sensitive data is regularly accessed or shared, such as in development, testing, or analytics.
For companies to get the most out of data masking for breach prevention, they need to follow certain best practices:
Know what data to mask
- Identify which data is sensitive and high priority for masking – things such as personal financial information, healthcare records, social security numbers, etc.
- Conduct risk assessments to know what data types need masking for legal and business reasons.
Use the right masking methods
- Different approaches such as substitution, shuffling, encryption, etc. are better for masking different types of data such as dates, IDs, names, addresses and more.
- Choose masking techniques that work with each data type to make the fake data look real.
Mask data at the source
- Mask data directly at the source systems where it is collected and enters the company.
- Don’t just mask databases – mask at apps, APIs, file systems, etc. This provides more complete coverage.
Mask data in real-time
- Mask sensitive data automatically in real-time as it is accessed and used across systems.
- Real-time masking doesn’t slow down operations or require downtime.
Use consistent masked data
- Keep data formats consistent and mask data consistently across all systems, so it remains usable.
- Ensure that masked values remain consistent across multiple uses to avoid operational issues.
Monitor and update masking
- Keep evaluating emerging sensitive data types and update masking rules to address them.
- Evolving regulations often require new data protections – keep masking updated.
Check masked data quality
- Test masked data to ensure adequate privacy protection and no reversibility back to originals.
- Assess whether masked data remains usable for your analytics and operations.
So in summary, intelligent planning, robust masking techniques, wide coverage, and ongoing governance ensures data masking effectively protects sensitive information against breaches.
How Does Data Masking Protect Against Data Breaches?
Unfortunately, data breaches are a growing threat as cyberattacks get more advanced and aggressive. When a company’s systems are hacked and data is stolen, it can significantly damage its business and reputation. Some recent famous breaches were on Yahoo, Equifax, Facebook, and many more big companies.
Data masking adds a layer of defense against data breaches in a few key ways:
-
Prevents theft of sensitive data:
If real confidential data is masked, hackers stealing the data only get fake masked values instead of actual private details. For instance, with a masked database, stolen credit card numbers would be useless fakes rather than active customer cards.
- Limits impact if non-production systems are breached:
Non-production systems such as for development and testing contain copies of real customer data. Masking this data prevents these systems from exposing full actual sensitive information if compromised.
- Protects outsourced or exposed datasets:
When sharing or exposing datasets externally or on cloud servers, masking provides an added level of safety even if the systems or transmissions are breached.
- Complies with breach notification laws:
Breach notification laws require informing customers if their private data is stolen. Masking may allow companies to avoid the substantial costs and reputational damage of mass breach notifications.
- Prevents stolen data from being used for fraud:
With masked fake data, bad actors cannot commit identity theft or financial fraud even if they get the data. Sensitive elements such as SSNs, account numbers, etc. won’t be real usable information.
Data masking limits damage in the event of a breach by preventing exposure of actual sensitive customer data. The fake masked data has no value to hackers or fraudsters.
Using Data Masking Without Disrupting Operations
Companies often worry that masking real production data may disrupt their business systems and operations. But modern data masking solutions use advanced techniques that allow companies to mask data without interrupting services or workloads:
Non-invasive, real-time masking
- Specialized tools can mask data on the fly in real-time as it is used, without affecting the original production systems at all.
No downtime or delays
- Real-time data masking avoids any downtime, maintenance windows, delays or latency in operations. Data is instantly masked as accessed.
Integrates seamlessly with existing systems
- Data masking integrates directly with databases, applications, analytics and other systems without requiring changes.
Scales across entire IT environments
- Automated masking can be applied across enormous production datasets and hundreds of systems efficiently.
Preserves operational performance
- Negligible performance overhead from real-time masking – systems run the same as before.
Maintains data usability
- Sophisticated algorithms maintain masked data quality so analytics and processes function normally.
Auditing and access controls
- Managing and controlling who can access/modify masking provides governance and auditing.
So with modern, optimized approaches, companies can mask even live production data without disrupting their business and technology operations.
Conclusion
Data breaches and hacks are growing threats that make protecting customer data a crucial priority. Data masking offers a proactive defense that reduces breach risks by substituting fake data for real sensitive information.
It protects data privacy and compliance while enabling business use cases such as development testing and outsourcing. Following best practices for identifying sensitive data, choosing effective masking techniques, masking comprehensively in real-time, and governance allows companies to implement data masking without business disruption.
With modern data masking, companies can dramatically limit their breach exposure and reduce risks for themselves and their customers. Although not a one-stop solution, data masking provides a robust additional layer of defense against the ever-growing dangers of data breaches.
FAQs
- Does data masking completely prevent breaches?
No, data masking reduces the damage from potential breaches but other security controls are still needed for full protection. It’s most effective as part of a defense-in-depth security strategy.
- When should data masking be implemented?
Ideally organizations should mask data proactively during application development, before launching any systems handling sensitive data. Adding masking to existing production systems is also recommended but more complex.
- Can masked data be unmasked to original values?
Properly masked data using strong irreversible techniques cannot be decoded back to original real data. The fake masked values permanently replace the actual sensitive data.